Darryl Strucko
Security Platform Product Prototypes
Designing and validating product concepts across threat intelligence, SOC workflows, and security data pipelines.
Built as working prototypes to explore product direction, integration patterns, and user experience — not just UI.
These prototypes explore how security platforms evolve from data ingestion to analyst decision-making and response.
01
Intelligence API + SecOps Platform Integration
Problem
Security teams struggle to prioritize and operationalize threat intelligence across multiple sources with inconsistent signal quality.
Approach
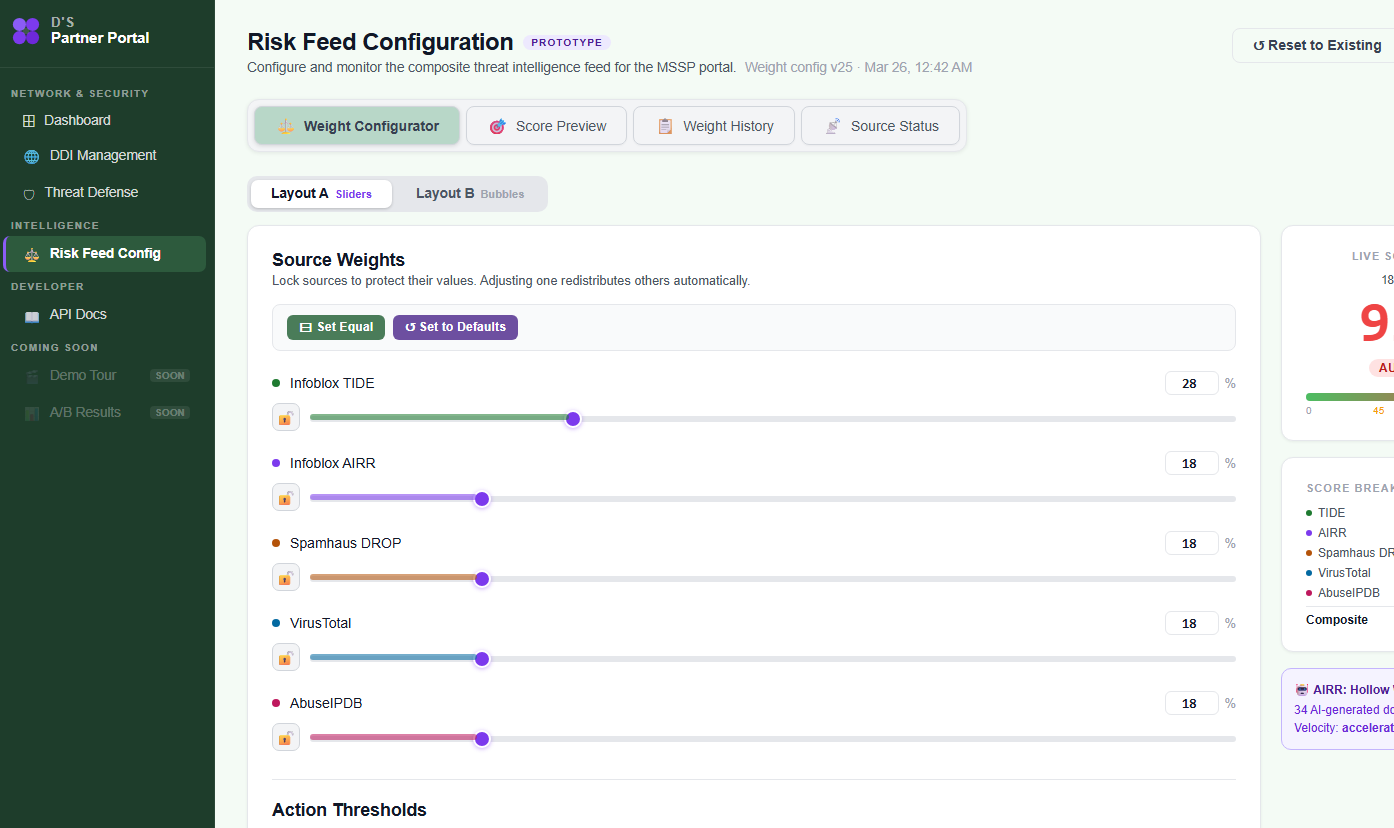
•Partner portal to configure and tune intelligence inputs
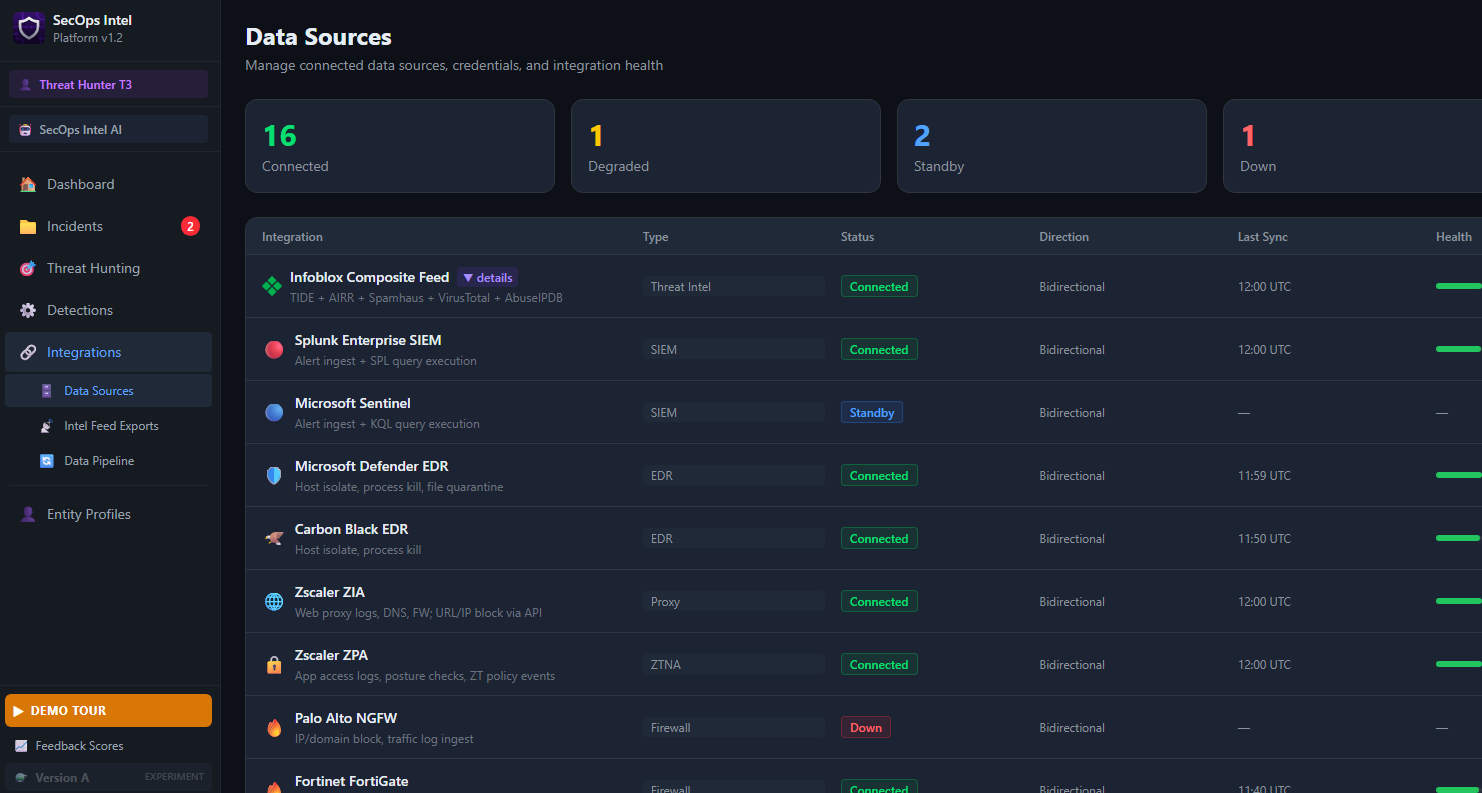
•SecOps portal to consume, prioritize, and act on that data
•Real-time synchronization via a shared data layer
Platform Architecture (simplified)
Configuration → Data Layer → Analyst Experience
What this demonstrates
•Platform thinking across producers and consumers of data
•API-driven integration between systems
•Real-time feedback loop between configuration and analyst outcomes
Key capabilities
•Tune and weight threat intelligence sources
•Surface prioritized signals in analyst workflows
•Push updates in real time across systems
Next steps
•Introduce automated response actions
•Expand correlation across multiple intelligence sources
•Add adaptive scoring based on analyst behavior
02
Security Operations Intelligence Platform
Problem
SOC teams operate across fragmented tools with limited visibility into coverage, prioritization, and analyst performance.
Approach
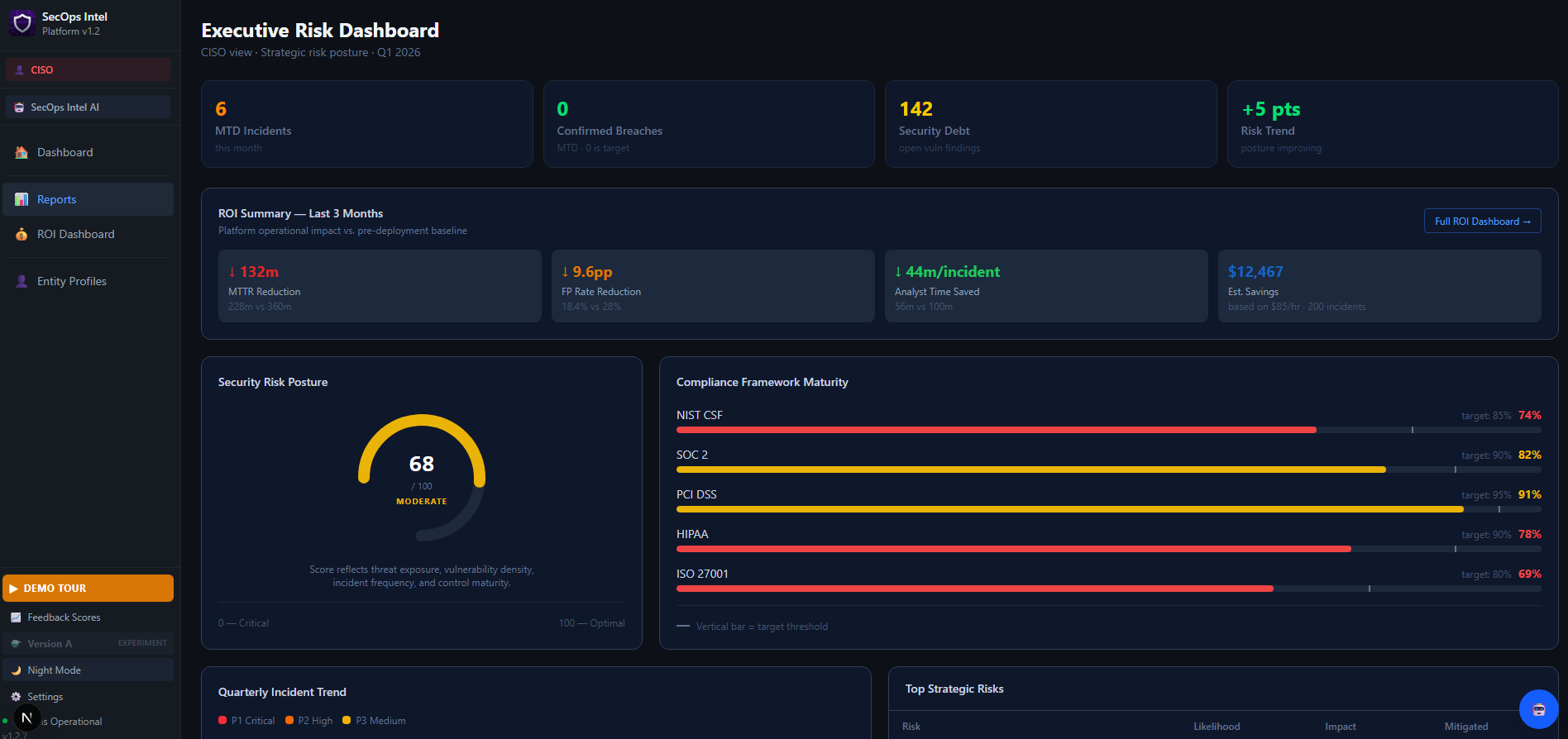
•Multi-persona platform spanning T1 analyst through CISO views
•Shared data with differentiated access across roles
What this demonstrates
•Multi-role product design across operational and executive users
•Alignment of tactical workflows with strategic visibility
•Structured access and data segmentation through an RBAC model
Key capabilities
•Triage, investigation, and proactive threat hunting workflows
•MITRE ATT&CK coverage tracking and SLA monitoring
•Guided demo and feedback capture for workflow validation
Next steps
•Deeper correlation across alerts and intelligence sources
•Executive-level risk summarization
•Integration with enforcement and response systems
03
Audit Logging for Incident Response
Problem
Capturing and reconstructing analyst actions during incidents is often inconsistent, making compliance and post-incident review difficult.
Approach
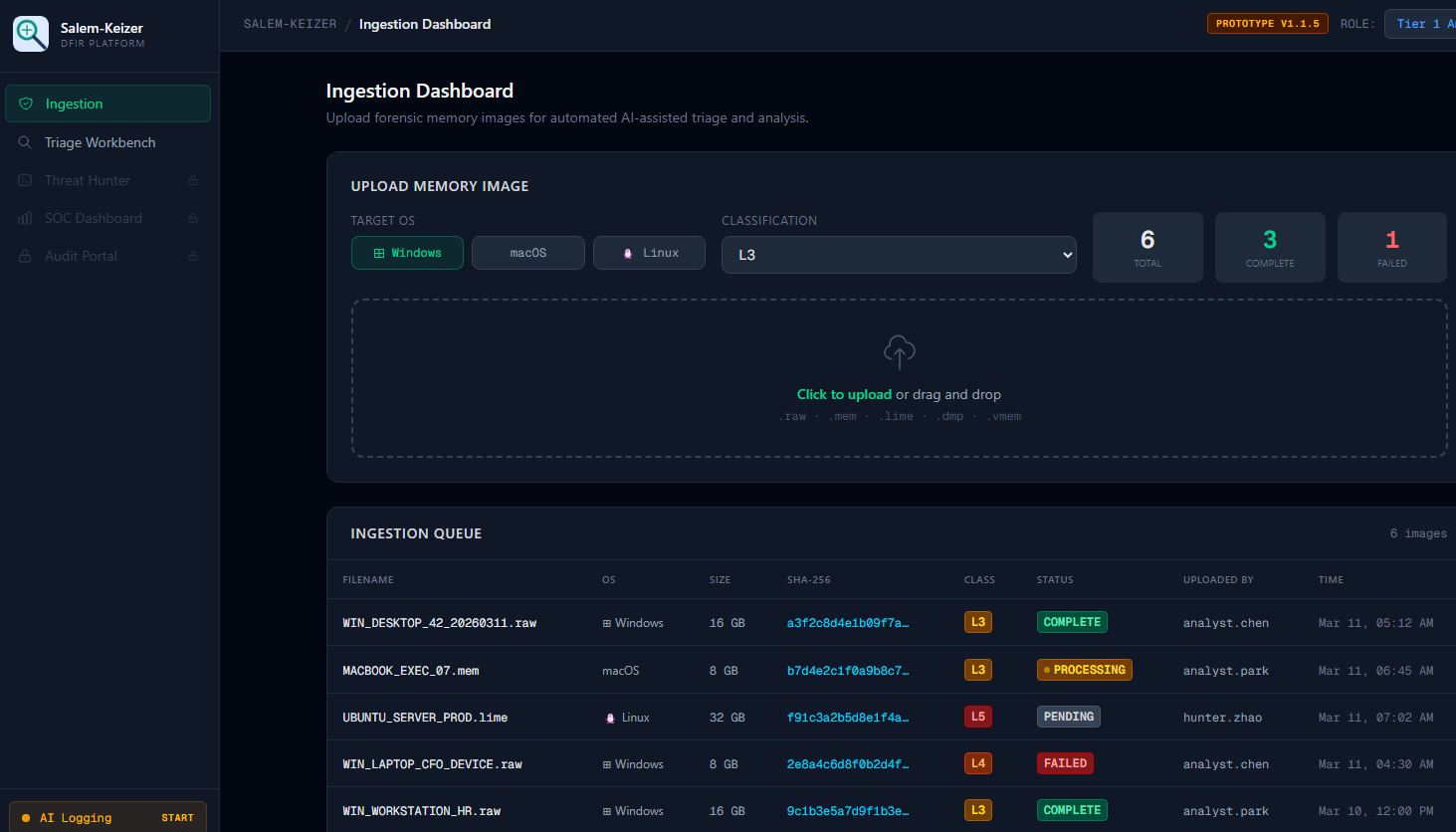
•DFIR-focused logging and export system
•Captures analyst actions in real time and generates structured outputs for compliance and review
What this demonstrates
•Alignment between product design and compliance requirements
•Data modeling for auditability and traceability
•Output design for compliance, reporting, and incident response teams
Key capabilities
•Capture analyst actions during investigation workflows
•Generate structured reports in multiple formats
•Export for compliance and post-incident analysis
Next steps
•Timeline reconstruction and visualization
•Integration with case management systems
•Automated compliance report generation
These are demonstration environments intended to showcase product direction and workflow design. No real customer or production data is used.
Built with Claude · Hosted on darrylstrucko.com